Congratulations on Your 14 IAM Tools
You've spent millions on disconnected identity tools. Meanwhile, basic account issues remain unsolved while vendors sell you AI-powered-blockchain-zero-trust-quantum-resistant solutions to problems you don't have.
IAM Spend: Where logic goes to die
The Economics of Delusion
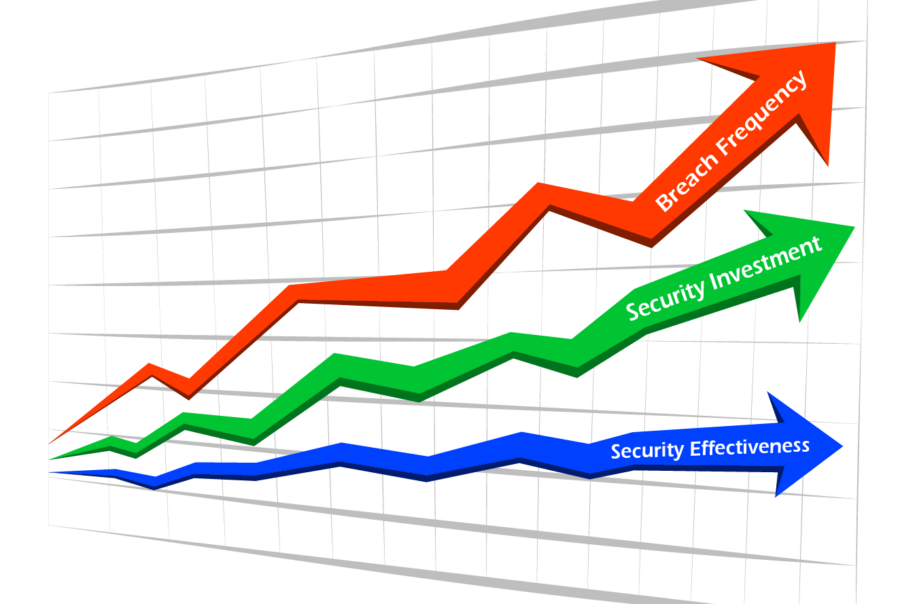
The IAM market defies logic: spending increases while security decreases. That's not a market—that's a money pit.
The IAM industry sells future value that never materializes, making crypto look like a safe investment.
NASA's Mars rover costs less than your IAM program. One explores space. The other can't reliably reset passwords.
You're buying Ferraris to use as doorstops. No other industry could survive with this level of waste.
14 different locks on your front door, each with its own locksmith who refuses to acknowledge the others exist.
Five vendors now control 67% of the market, yet breaches continue to rise. This isn't coincidence—it's causation.
You're paying for duct tape consultants to integrate 2025 tools with 1997 systems at $300/hour.
IAM Tool Utilization
Why Your Identity Security Stack Is a Money Pit
The Ferrari Parts on a Toyota Problem
Your CISO buys premium tools for advanced threats while basic service accounts from 2018 remain your biggest risk. It's like installing a high-tech alarm while leaving your door unlocked.
The Platform Fallacy
Investment firms acquire point solutions and force them into a "platform" that doesn't work together. They sell more licenses but won't help you implement them effectively.
The Rollup Acquisition Trap
Vendors under pressure to hit investor targets acquire customer bases, not strategic solutions. The result: duplicate functionality and confused users.
The Vendor Yacht Fund
Five vendors control 67% of the market, yet enterprises use more tools than ever. Consolidation has created more complexity, not less.
The Legacy Tech Burden
Most leading identity vendors were designed decades ago and can't solve today's hybrid challenges. Old and new technologies create silos that can't communicate.
The Futurism Distraction
76% of identity startups focus on "next-gen" problems rather than today's challenges. While AI and zero-trust get attention, your forgotten service accounts remain the actual risk.
Time to Escape the Security Theater
When your unmanaged service account gets compromised, showing the board your vendor roster won't help. It's time for a different approach.
Get a Reality Check